In an era where cyberattacks are growing more sophisticated by the day, traditional perimeter-based security models are no longer enough. Zero Trust is a modern security framework for organizations of every size. Whether you are a business owner, IT professional, or cybersecurity enthusiast, understanding this is essential to protecting your digital assets in today’s threat landscape.
This comprehensive guide explains what Zero Trust is, why it matters, its core principles, and most importantly, how to implement it in your organization step by step.
What Is Zero Trust?
Zero Trust is a cybersecurity framework. Its simple but powerful principle is: “Never trust, always verify”. Unlike traditional security models that assume everything inside a corporate network is safe. It treats every user, device, and network connection as a potential threat, regardless of whether they are inside or outside the organizational perimeter.
The concept of Zero Trust was first introduced by John Kindervag, a former analyst at Forrester Research, in 2010. Since then, it has evolved from a niche concept into a widely adopted strategy endorsed by governments and enterprises worldwide, including the U.S. federal government’s mandate for this architecture.
Zero Trust is not a product you buy; it is a strategy you implement. It fundamentally changes how organizations think about security.
Why Does Zero Trust Matter?
The traditional “castle-and-moat” security model assumed that threats came from outside the network. Once a user or device was inside the network, they were trusted by default. This approach has proven dangerously inadequate for several reasons:
- Remote work and cloud adoption have dissolved the traditional network perimeter.
- Insider threats — whether malicious or accidental represent a significant portion of data breaches.
- Stolen credentials allow attackers to move laterally inside networks undetected.
- Third-party vendors and supply chain attacks can compromise trusted network segments.
It addresses all of these vulnerabilities by requiring continuous verification for every access request, no matter where it originates. According to IBM’s Cost of a Data Breach Report 2023, organizations that have deployed this architecture saved an average of $1.5 million in breach costs compared to those without it.
Core Principles of Zero Trust
It is built on several fundamental principles that collectively eliminate implicit trust from the security equation:
1. Verify Explicitly
It requires that every access request be authenticated, authorized, and continuously validated. This means leveraging multiple data points: user identity, device health, location, and behavior before granting access to any resource.
2. Use Least-Privilege Access
Here, users and systems are granted only the minimum level of access they need to perform their specific tasks. This principle, known as least-privilege access, minimizes the blast radius of a potential breach.
3. Assume Breach
It operates under the assumption that a breach has already occurred or will occur. Rather than trying to build an impenetrable barrier, it focuses on limiting the damage by segmenting access, encrypting communications, and monitoring all traffic continuously.
4. Micro-Segmentation
It divides the network into smaller, isolated segments so that even if one area is compromised, attackers cannot move freely across the entire system. Each segment requires its own authentication and authorization.
5. Continuous Monitoring and Validation
It is not a one-time configuration. It demands real-time monitoring of all network activity, user behavior, and device health. Any anomaly triggers a re-verification or automatic revocation of access.
Key Components of a Zero Trust Architecture
It is a comprehensive architecture with several interconnected components. Understanding these building blocks is critical before beginning your implementation journey.
Identity and Access Management (IAM)
At the heart of Zero Trust is a robust Identity and Access Management system. It relies on strong identity verification, typically Multi-Factor Authentication (MFA), to ensure that only legitimate users gain access to resources.
Device Security and Endpoint Management
It requires that every device attempting to access resources meet specific security standards. Endpoint Detection and Response (EDR) tools and Mobile Device Management (MDM) solutions play a critical role in enforcing device policies.
Network Micro-Segmentation
In this network, traffic is segmented and isolated. Software-defined perimeters (SDP) and next-generation firewalls are commonly used tools in this architecture to enforce granular network access controls.
Data Security
It demands that sensitive data be encrypted both in transit and at rest. Data Loss Prevention (DLP) tools help enforce its policies by monitoring and controlling how sensitive data is accessed and shared.
Application Security
In this model, applications are secured at the application layer rather than the network layer. This means implementing Zero Trust access controls for each application individually, regardless of whether it is hosted on-premises or in the cloud.
Security Information and Event Management (SIEM)
SIEM platforms are essential for this because they aggregate and analyze security data from across your entire environment, enabling real-time detection of threats and anomalies.
Learn how password spraying attacks work and discover simple steps to strengthen your security.
How to Implement Zero Trust: A Step-by-Step Guide
Implementing Zero Trust is a journey, not a destination. It does not require ripping out existing infrastructure overnight. Instead, its implementation is a phased, strategic process that gradually matures your organization’s security posture. Here is a practical roadmap to get started.
Step 1: Define the Protect Surface
Before you can implement, you need to know what you are protecting. Unlike trying to define the massive attack surface, it focuses on identifying your “protect surface,” the most critical data, assets, applications, and services (DAAS) your organization relies on.
- Identify sensitive data (PII, financial records, intellectual property).
- Map critical business applications and services.
- Catalog all connected devices, endpoints, and IoT systems.
- Understand data flows: who accesses what, from where, and when.
Step 2: Map Transaction Flows
It requires a deep understanding of how your data and applications interact. Map every transaction flow to understand how traffic moves through your network. This mapping process reveals hidden dependencies, over-privileged accounts, and unnecessary access paths that need to be eliminated.
Step 3: Architect a Zero Trust Network
With yours protect surface and transaction flows defined, you can begin designing your network architecture. Key design decisions include:
- Deploying a Software-Defined Perimeter (SDP) to hide resources from unauthorized users.
- Implementing micro-segmentation to isolate workloads and limit lateral movement.
- Replacing traditional VPNs with Zero Trust Network Access (ZTNA) solutions.
- Positioning a next-generation firewall as a Zero Trust enforcement point.
Step 4: Create Zero Trust Policies
Once the architecture is in place, create granular access policies that govern who can access what resources, under what conditions, and for how long. Effective policies are built around the “who, what, when, where, why, and how” of every access request.
Its policies should be as specific as possible. For example, instead of allowing a user access to an entire database, a policy would allow access only to the specific table they need for a defined period.
Step 5: Deploy Multi-Factor Authentication (MFA)
Multi-Factor Authentication is a non-negotiable component. MFA ensures that even if credentials are stolen, attackers cannot gain access without the second verification factor. It goes beyond basic MFA by implementing adaptive authentication, adjusting the level of authentication required based on the risk level of the access request.
Step 6: Implement Least-Privilege Access Controls
Audit all existing user accounts, service accounts, and third-party access permissions. Under Zero Trust principles, revoke all excessive privileges and enforce a strict least-privilege policy. Role-Based Access Control (RBAC) and Attribute-Based Access Control (ABAC) are powerful tools for enforcing least-privilege policies at scale.
Step 7: Secure and Monitor All Workloads
It requires continuous monitoring of all workloads on-premises, cloud, and hybrid environments. Deploy a SIEM platform and integrate it with your architecture to enable:
- Real-time threat detection and automated incident response.
- User and Entity Behavior Analytics (UEBA) to spot anomalous activity.
- Comprehensive audit logs for compliance and forensic purposes.
- Automated policy enforcement when Zero Trust violations are detected.
Step 8: Automate and Orchestrate Zero Trust Policies
Manual enforcement of policies at enterprise scale is not feasible. Leverage Security Orchestration, Automation, and Response (SOAR) platforms to automate policy enforcement, threat response, and compliance reporting. Automation is what makes this scalable and sustainable over time.
Step 9: Continuously Monitor, Audit, and Improve
Zero Trust is a living framework. Conduct regular audits to assess your Zero Trust maturity, identify gaps, and adapt policies to emerging threats. Use the NIST Zero Trust Architecture framework (NIST SP 800-207) as a benchmark for measuring your program’s progress.
Zero Trust vs. Traditional Security: Key Differences
Understanding how Zero Trust differs from the traditional perimeter-based security model clarifies why it has become the preferred approach for modern organizations.
Traditional Security
- Trust is implicit once inside the network perimeter.
- Assumes the internal network is a safe zone.
- Limited visibility into the lateral movement of threats.
- Single-factor authentication is often sufficient.
- Static access permissions that rarely change.
Zero Trust Security
- Requires explicit verification for every request.
- Treats the internal network as untrusted by default.
- Provides granular visibility across all traffic.
- Mandates MFA and continuous authentication.
- Enforces dynamic, context-aware access policies.
Common Frameworks and Standards
Several established frameworks can guide your Zero Trust implementation:
NIST SP 800-207 (Zero Trust Architecture)
Published by the National Institute of Standards and Technology, NIST SP 800-207 is the most widely referenced framework. It defines the core components, deployment models, and use cases for this architecture in federal and enterprise environments.
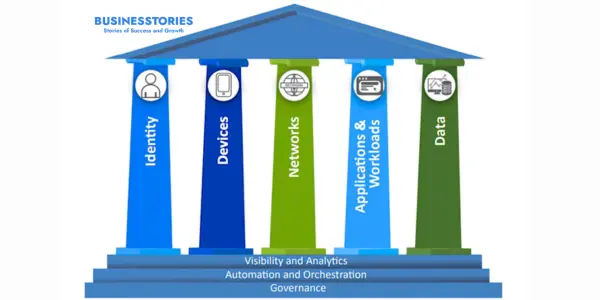
CISA Zero Trust Maturity Model
The Cybersecurity and Infrastructure Security Agency (CISA) Zero Trust Maturity Model provides a phased roadmap for federal agencies and is equally valuable for private sector organizations to gradually mature their Zero Trust capabilities across five pillars: Identity, Devices, Networks, Applications, and Data.
Google BeyondCorp
Google’s BeyondCorp is one of the earliest and most famous real-world implementations of Zero Trust. BeyondCorp demonstrates how it can enable secure access to applications without a traditional VPN, relying entirely on device and user identity verification.
Microsoft Zero Trust Framework
Microsoft’s Zero Trust framework integrates with Azure Active Directory and Microsoft Defender to provide a practical, cloud-native implementation guide suitable for organizations of all sizes.
Challenges While Implementing
While it offers transformative security benefits, its implementation is not without challenges. Being aware of these obstacles helps organizations plan their Zero Trust journey more effectively.
- Complexity: It requires significant architectural changes and cross-team coordination.
- Legacy Systems: Older applications and systems may not support Zero Trust-compatible authentication protocols.
- Cost: Initial implementation requires investment in new tools and training.
- Cultural Resistance: Employees may resist stricter access controls if they are not properly educated.
- Vendor Lock-In: Many solutions are proprietary, creating dependency risks.
The key to overcoming these challenges is to approach Zero Trust as an incremental journey, starting with your highest-value assets and gradually expanding controls across the organization.
Zero Trust Best Practices
To maximize the effectiveness of your Zero Trust program, follow these industry-proven best practices:
- Start with Identity: Identity is the cornerstone of Zero Trust. Prioritize deploying strong IAM and MFA before expanding Zero Trust to other areas.
- Educate Your Team: It is as much a cultural shift as a technical one. Invest in employee security awareness training aligned with Zero Trust principles.
- Prioritize High-Value Assets: Begin your Zero Trust rollout with the most sensitive data and critical applications to maximize early security gains.
- Leverage Automation: Use automation to enforce policies consistently and at scale without overburdening security teams.
- Adopt a Zero Trust Vendor Ecosystem: Choose security vendors that natively support its principles and integrate well with your existing stack.
- Measure and Report: Establish Zero Trust KPIs and metrics to track your progress and demonstrate the ROI of your investments to leadership.
The Future of Zero Trust
Zero Trust is not just a trend; it is the future of cybersecurity. As organizations continue their digital transformation journeys, it will become the default security model rather than the exception. Several emerging developments are shaping the future of Zero Trust:
- AI and Machine Learning: AI-driven analytics will be enhanced by enabling more accurate, real-time risk assessments and automated policy adjustments.
- Zero Trust for IoT: As the Internet of Things expands, its principles will be extended to secure billions of connected devices.
- Zero Trust in the Cloud: Cloud-native solutions are making it easier for organizations of all sizes to implement this without massive infrastructure investments.
- Regulatory Requirements: Governments worldwide are increasingly mandating architecture for public sector and critical infrastructure organizations.
Conclusion:
Zero Trust is no longer an optional security upgrade — it is a business imperative. The question is not whether your organization should adopt it, but how quickly you can begin your journey.
By implementing, you dramatically reduce your attack surface, limit the damage from potential breaches, and build a security posture resilient enough to withstand today’s and tomorrow’s threats. It may require investment and effort, but the cost of a breach far outweighs the cost of implementation.
Start your journey today. Begin with your most critical assets, build a clear roadmap, and commit to the continuous improvement that Zero Trust demands. In a world where cyber threats are constant and evolving, it is the security strategy that keeps your organization one step ahead.
Explore the advantages of adopting cloud-based solutions for modern businesses.